Is it possible to fetch CVEs based on a software name and/or it’s associated version via an API call to Vulmatch? If yes, what is the endpoint of the API call and preferably the link to it’s documentation would be helpful.
Yes. Let me break it down
software name and/or it’s associated version
In Vulmatch we use CPEs to represent software.
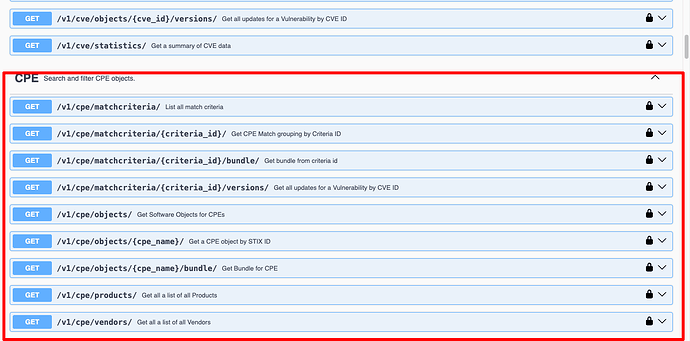
If you view the API docs, you will see the ability to search for CPEs in various ways.
The CPE object search is where you want to start. It accepts a lot of optional filters to find the softwares you want
curl -X 'GET' \
'https://api.vulmatch.com/v1/cpe/objects/?product=chrome&vendor=google' \
-H 'accept: application/json' \
-H 'API-KEY: HIDDEN'
Which will return a response with all software type objects that match the query, e.g
{
"page_size": 500,
"page_number": 1,
"page_results_count": 500,
"total_results_count": 9245,
"objects": [
{
"cpe": "cpe:2.3:a:google:chrome:103.0.5053.0:*:*:*:*:*:*:*",
"extensions": {
"extension-definition--82cad0bb-0906-5885-95cc-cafe5ee0a500": {
"extension_type": "toplevel-property-extension"
}
},
"id": "software--004a22d9-44f1-5fb3-8d1e-ca7ab979be9d",
"name": "Google Chrome 103.0.5053.0",
"object_marking_refs": [
"marking-definition--94868c89-83c2-464b-929b-a1a8aa3c8487",
"marking-definition--152ecfe1-5015-522b-97e4-86b60c57036d"
],
"spec_version": "2.1",
"swid": "EA548ED5-0EEC-4FFF-BECC-A878730D9DE9",
"type": "software",
"vendor": "google",
"version": "103.0.5053.0",
"x_cpe_struct": {
"cpe_version": "2.3",
"part": "a",
"vendor": "google",
"product": "chrome",
"version": "103.0.5053.0",
"update": "*",
"edition": "*",
"language": "*",
"sw_edition": "*",
"target_sw": "*",
"target_hw": "*",
"other": "*"
},
"x_created": "2022-09-07T17:07:26.587Z",
"x_modified": "2022-09-21T15:23:58.053Z",
"x_revoked": false
},
Taking a specific CPE ID, you can then get a bundle of all Vulnerabilities linked to it
curl -X 'GET' \
'https://api.vulmatch.com/v1/cpe/objects/cpe%3A2.3%3Aa%3Agoogle%3Achrome%3A103.0.5053.0%3A%2A%3A%2A%3A%2A%3A%2A%3A%2A%3A%2A%3A%2A/bundle/?types=vulnerability' \
-H 'accept: application/json' \
-H 'API-KEY: HIDDEN'
{
"page_size": 500,
"page_number": 1,
"page_results_count": 500,
"total_results_count": 823,
"objects": [
{
"created": "2025-06-03T00:15:21.043Z",
"created_by_ref": "identity--8869d5c4-7fbe-5af3-b0b2-13f4d10d8f40",
"description": "Out of bounds read and write in V8 in Google Chrome prior to 137.0.7151.68 allowed a remote attacker to potentially exploit heap corruption via a crafted HTML page. (Chromium security severity: High)",
"extensions": {
"extension-definition--2c5c13af-ee92-5246-9ba7-0b958f8cd34a": {
"extension_type": "toplevel-property-extension"
},
"extension-definition--ec658473-1319-53b4-879f-488e47805554": {
"extension_type": "toplevel-property-extension"
}
},
"external_references": [
{
"source_name": "cve",
"url": "https://nvd.nist.gov/vuln/detail/CVE-2025-5419",
"external_id": "CVE-2025-5419"
},
{
"source_name": "cwe",
"url": "https://cwe.mitre.org/data/definitions/CWE-125.html",
"external_id": "CWE-125"
},
{
"source_name": "[email protected]",
"description": "Release Notes",
"url": "https://chromereleases.googleblog.com/2025/06/stable-channel-update-for-desktop.html"
},
{
"source_name": "[email protected]",
"description": "Permissions Required",
"url": "https://issues.chromium.org/issues/420636529"
},
{
"source_name": "af854a3a-2127-422b-91ae-364da2661108",
"description": "Third Party Advisory",
"url": "https://msrc.microsoft.com/update-guide/vulnerability/CVE-2025-5419"
},
{
"source_name": "134c704f-9b21-4f2e-91b3-4a467353bcc0",
"description": "US Government Resource",
"url": "https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2025-5419"
},
{
"source_name": "vulnStatus",
"description": "Analyzed"
}
],
"id": "vulnerability--209d33a5-48a8-5aeb-a4c2-043f5cb7a259",
"modified": "2025-10-24T14:06:46.073Z",
"name": "CVE-2025-5419",
"object_marking_refs": [
"marking-definition--94868c89-83c2-464b-929b-a1a8aa3c8487",
"marking-definition--562918ee-d5da-5579-b6a1-fae50cc6bad3"
],
"spec_version": "2.1",
"type": "vulnerability",
"x_cvss": {
"v3_1": [
{
"base_score": 8.8,
"base_severity": "HIGH",
"exploitability_score": 2.8,
"impact_score": 5.9,
"source": "134c704f-9b21-4f2e-91b3-4a467353bcc0",
"type": "Secondary",
"vector_string": "CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H"
}
]
},
"x_opencti_cisa_kev": true,
"x_opencti_cvss_base_score": 8.8,
"x_opencti_cvss_base_severity": "HIGH",
"x_opencti_cvss_vector_string": "CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H",
"x_opencti_epss_percentile": 0.78767,
"x_opencti_epss_score": 0.01262
},